FIN SCAN is one of the port scanning methods in Nmap, which uses the sheer stupidity of old and stateless firewalls. In fact, when it comes to FIN Scan, our Port Scanner software sends a packet with a flag in the form of FIN meaning the end of the session to the destination firewall or host. If no response is received, it means that the port is open, and if the return is RST//ACK, it means that the server port is closed. In this article, we try to teach you to step by step How to Scan Ports With FIN SCAN On Nmap. You can visit the packages available in Eldernode if you wish to purchase a VPS server.
Table of Contents
How to Scan Ports With FIN SCAN On Nmap
As you know, in the Port Scanning process, the Three-way Handshake process that TCP does is very useful. So when it comes to FIN Scan, naturally you have to think that it means a TCP Finish flag that is used to end a TCP Session.
This scan method is still responsible for scanning services behind stateless firewalls. When stupid firewalls see the FIN Flag, they think to themselves that there probably was a session before and now it wants to end. So they allow the data packet to pass! Today, this type of scan is not very suitable for our work and has been replaced by more advanced port scans, but in any case, this type of scan can also be used for DOS attacks.
In the continuation of this article, join us to teach you how to Scan Ports With FIN SCAN On Nmap.
What is FIN SCAN?
The Nmap FIN scan comes in handy in such circumstances. The standard use of a FIN packet is to terminate the TCP connection, typically after the data transfer is complete. Instead of an SYN packet, Nmap initiates a FIN scan by using a FIN packet. Since there is no earlier communication between the scanning host and the target host, the target responds with an RST packet to reset the connection. However, by doing so, it reveals its presence.
The FIN SCAN method works by first sending a FIN scan to a packet that never happens in the real world. It sends a packet with the FIN flag set without first establishing a connection with the target. Again, if no packet is received, the port is considered open and if an RST packet is received, the port is considered closed.
In the next section, join us to teach you How to Scan Ports With FIN SCAN On Nmap with an example.
Scan Ports With FIN SCAN On Nmap
In this section, we want to introduce you to how to Scan Ports With FIN SCAN On Nmap. Note that using this type of scan is simple. Just use the -sF option. You can use the following command to scan ports in Nmap:
nmap -sF Your_IP_AddressConsider the following example:
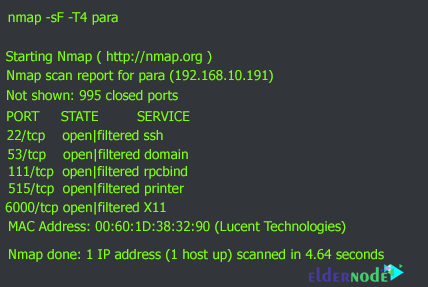
nmap -sF -T4 paraThe output of the above command will be as follows. As you can see, after executing the FIN Scan command, it is clear that 5 ports are open. (as open | filtered). These open ports are ports 22, 53, 111, 515, and 6000.
It should note that With a modern stateful firewall, a FIN scan should not produce any extra information. However, it is still widely using in some cases. Consider the following example:
nmap -sF -T4 docsrv.domain.com
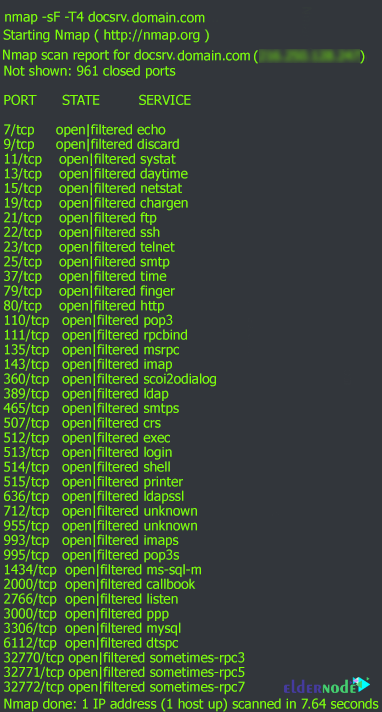
As you can see in the output above, 961 ports are closed but 39 ports are open.
Conclusion
In this article, we tried to teach you to step by step How to Scan Ports With FIN SCAN On Nmap with an example. You can refer to our articles on How to Scan ports using Connect Scan and stealth scan on Nmap if you wish.