Never stop caring about the security. Sqlninja is a SQL Injection tool. The SQL Injections are vulnerable, Sqlninja exploits web applications and gets a running shell on the remote host. The web applications use Microsoft SQL Server as its back-end. Sqlninja provides remote access to the vulnerable DB server. When a SQL Injection vulnerability is discovered, the Sqlninja should be used by penetration testers to help and automate the process of taking over a DB server. In other words, once it discovers an SQL injection, will automate the exploitation process. In this article, we are going to present Introducing And How To Install Sqlninja On Kali Linux. Choose your preferred package on Eldernode and purchase your own Linux VPS.
Table of Contents
Introducing Sqlninja On Kali Linux
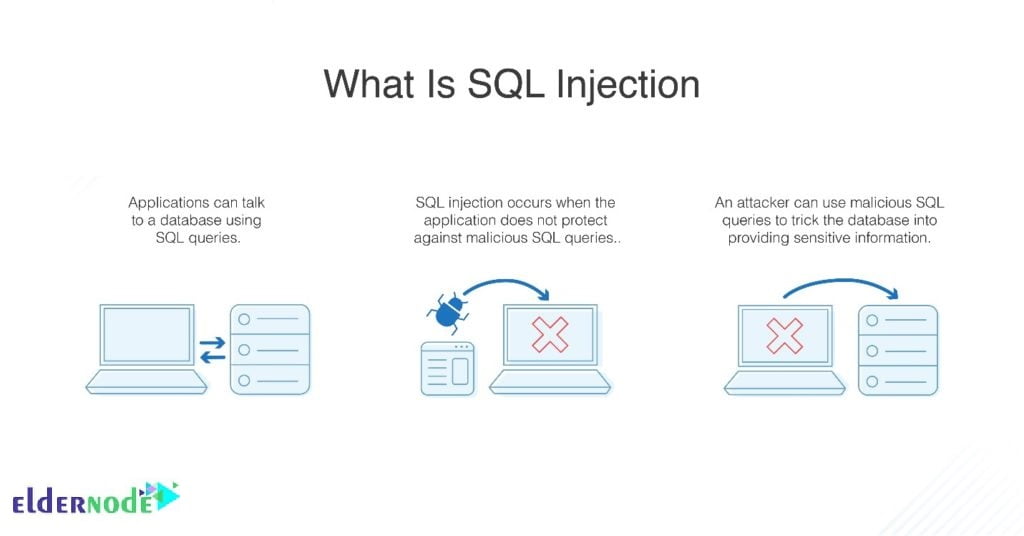
Even when the general environment is hostile, Sqlninja provides the attackers remote access to the vulnerable database. Penetration testers use it to check for SQL injection vulnerabilities and analyze the security. SQL injection is the way of most common attacks on databases which is really harmful to web applications. So, you need to secure your web application to protect your information.
Sqlninja Requirements
Sqlninja is completely written in Perl and is a Perl script that needs a number of Perl libraries to function properly. So, you need to just install Perl itself and its modules such as:
- NetPacket
- Net-pcap
- Net-DNS
- Net-RawIP
- IO-Socket-SSL
- Net-Pcap
- DBI
- Net-RawIP
In case you wish to use the Metasploit attack mode, you need to provide Metasploit Framework 3 on your box. And also if you want to use the VNC payload, you need a VNC client.
You should run the Sqlninja on any Unix based platform with a Perl interpreter to let all needed modules be installed. Sqlninja is available for Unix Operating System and has successfully tested on:
- Linux
- FreeBSD
- Mac OS X
- IOS
Please be aware that, Sqlninja does not run on Windows. Sqlninja is under GNU General Public License version 3.0 (GPLv3). The new version, 0.2.999-alpha1 is released and data extraction via WAITFOR and DNS tunnel, plus vbscript-based is added. Also, the 0.2.6.r1 is the stable version of Sqlninja which lacks the data extraction module that is available on alpha1.
Sqlninja Features
1- Time-based or via a DNS tunnel, Sqlninja extracts the data.
2- Sqlninja provides a fingerprint of the remote SQL server. It includes the version, the user performing the queries. user privileges, xp_cmdshell availability, and DB authentication mode.
3- To obtain graphical access to the remote DB server, Sqlninja provides integration with Metasploit3. It goes through a VNC server injection or just to upload Meterpreter.
4- Bruteforce of ”sa” password in dictionary-based and incremental.
5- If the original version has been removed, it creates a custom xp_cmdshell
6- Without needing any FTP/TFTP and via vbscript or debug.exe, Sqlninja could upload netcat using only normal HTTP requests. (Sqlninja uses a new way to configure the HTTP requests and the relative injection string when version 0.2.6 released)
7- Direct and reverse bind shell, both TCP and UDP. (The DB server can resolve external hostnames)
8- TCP/UDP portscan from the target SQL Server to the attacking machine, in order to find a port that is allowed by the firewall of the target network and use it for a reverse shell.
9- Sqlninja escalates privileges for the sysadmin group if founds ”sa” password.
10- Sqlninja considered evasion techniques to confuse a few IDS/IPS/WAF.
11- Sqlninja supports for CVE-2010-0232, to escalate the privileges of sqlservr.exe to SYSTEM.
SQL Injection attacks
SQL injection is one of the most dangerous attacks on web applications. And has placed in the list of Top 10 Web Application Security Threats. When do SQL injection attacks occur? If an application processes the user-provided data without validation, SQL injection occurs. So, SQL injection can let hackers access database content or remote commands in the system. Companies and organizations use SQL servers as a database to store confidential information. So, it is clear why hackers choose to attack it. It could result in a situation that hackers take control of the server that hosts the database. If you need to know what factors are efficient in SQL injection attacks, have a look at the below list:
1- Where the vulnerability occurs in the code.
2- How vulnerability lets hackers act.
3- The access level of the damaged application to the server database.
Tutorial Install Sqlninja On Kali Linux
The database helps both users and servers by providing wide features as data input and storage, retrieval of large information, and so on. Hackers and Pentesters are always trying to catch an opportunity to find a gap in the security of the database. So, you can use the Sqlninja to control the database server through a SQL injection flaw. Now that you have been familiar with Sqlninja and SQL injection, let’s see how to install Sqlninja on Kali Linux Server.
Install Sqlninja On Kali Linux [Complete]
Run the below command to install:
sudo apt-get install sqlninjaNow, you have installed Sqlninja and all needed packages.
To install all dependencies, use the following command:
sudo apt-get installYou can find it in Kali by navigating to Applications > Database Assessments.
How to uninstall Sqlninja on Kali Linux
Anytime you need to remove the Sqlninja, you can run the command below to do this:
sudo apt-get remove sqlninjaIn this way, you can remove just the Sqlninja package itself.
Also, you can use the following command to uninstall Sqlninja and its dependencies.
sudo apt-get remove --auto-remove sqlninjaUsing the command below helps you purge your config/data too:
sudo apt-get purge sqlninjaOR,
sudo apt-get purge --auto-remove sqlninjaIn this way, you will delete your local/config files for Sqlninja.
That’s that. By reaching this point you have successfully finished this guide. In case you are going to buy a dedicated server and security is your target, follow our articles security to become an expert free and quick.
Conclusion
In this article, you learned about Introducing And How To Install Sqlninja On Kali Linux. Please note that you are not using Sqlninja as a tool for detecting the existence of an injection flaw, but as you read in this guide, it is used to exploit the flaw to shell access to the database server.