
Site security training in IIS. Internet Information Services (IIS) is a flexible and general purpose web server from Microsoft. IIS runs on Windows systems to deliver requested HTML pages or files. When investigating site infections or defacing on a Windows VPS Server, the most common root cause is poor file security or poor configuration choices when it comes to how IIS should access file content. The easiest way to prevent this is to start with a secure site.
Setting up a website in IIS is exceedingly easy, but several of the default settings are not optimum when it comes to security or ease of management. Some practices that used to be considered necessary or standards are no longer or were never necessary, to begin with.
We recommend that you follow these steps to set up a website to ensure that it is set up correctly and securely.
Table of Contents
Add site to IIS
1. To add a website in IIS, open up the IIS Manager.
2. Right-click on Sites.
3. Select Add Website.
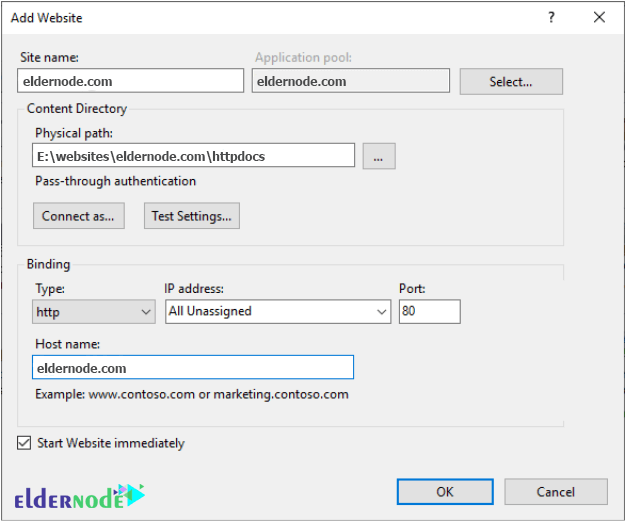
We typically recommend using the domain name as the “Site name” for easy identification.
4. Under Physical path, you will need to supply the path to where your website content is located or use the “…” to navigate to and select the folder.
Note: Configuration options under “Connect as…” and “Test Settings…” do not need to be modified.
It is best to leave IP addresses set to All Unassigned and type the domain name you plan to host in the Host name field. You can only supply one value here.
Additional host names can be added after creating the site by right-clicking on the site and going to Bindings.
Depending on your needs, you may opt to select HTTPS instead of HTTP.
Site security training in IIS
How to Set the Anonymous User
That is all you need to do to set up a site in IIS.
The site may or may not work, and the security settings on the site are not optimum.
The next step in securing your site is to configure the IIS user that will access your files. To do this, you will need to change the associated Anonymous user and make a few security changes on the website’s content folder.
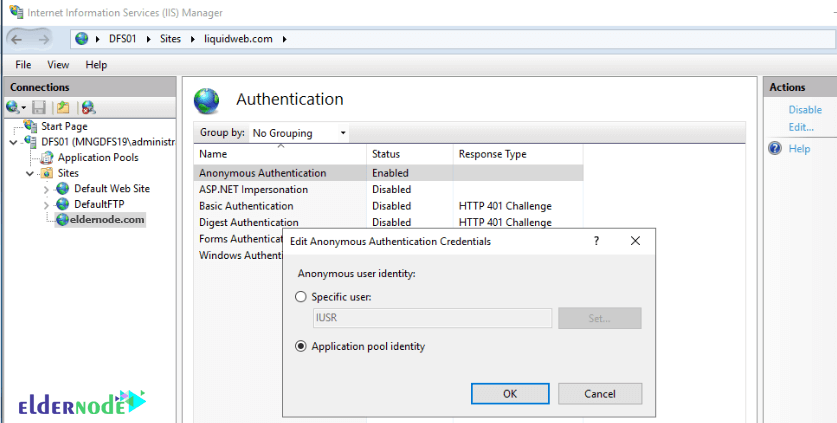
1. In IIS, select your new site on the left.
2. In the main window double click on Authentication.
3. Select Anonymous Authentication.
4. Click “Edit…” on the right action bar.
What is IUSR in IIS?
A new site in IIS utilizes the IUSR account for accessing files. This account is a built-in shared account typically used by IIS to access file content. This means that it will use the application pool’s identity (user) to access file content.
It may be okay to leave this configured if you only plan on hosting one domain; however, when it comes to hosting multiple domains, this is not secure as it would then be possible for any site using the same account to access files from another site.
As a standard practice, we recommend switching away from using the IUSR account for sites, and instead of selecting “Application pool identity” and clicking OK.
You could manually create a user on the system for each site. You need to manage credentials for an additional user, need to configure permissions for two users (the anonymous user and the application pool user) and possible complications with password complexity and rotation requirements your server or organization may have.
There is nothing further you need to configure in IIS in terms of security.
Site security training in IIS
Let’s take a look at the application pool settings really quickly. To check the settings on the application pool, in IIS do the following:
1. Select Application Pools on the left menu.
2. Then select the application pool for the site you created (typically the same name as the name of the site).
3. Click “Advanced Settings…” on the right action bar.
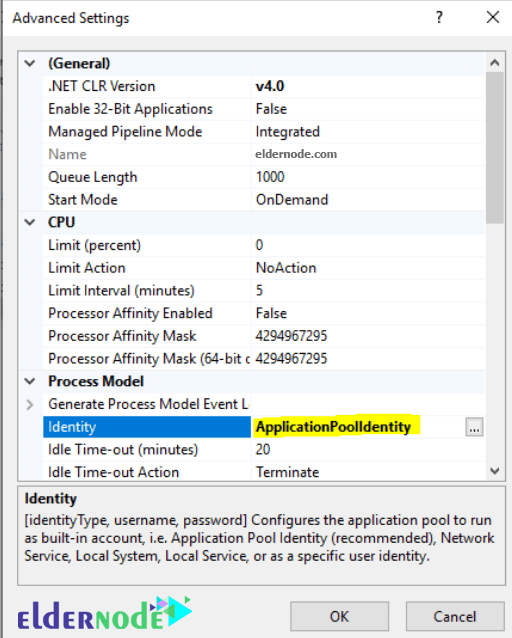
In here, the related setting is the identity, which by default is ApplicationPoolIdentity. This means to access file content, IIS and the associated application pool will use a hidden, dynamic user based on the name of the application pool to access files.
This user has no associated password, can only be used by IIS, and only has access to files specifically granted to it.
As such, it removes the requirement of managing system users and credentials.
How to Set Folder Permissions in IIS
The ApplicationPoolIdentity user has very few permissions, so the next and last step is to ensure that the website files have proper security settings set on them.
1. Browse through your file system and find the folder where you plan on hosting your site’s files.
2. Right-click on the folder and go to properties.
3. In the properties interface, select the Security tab.
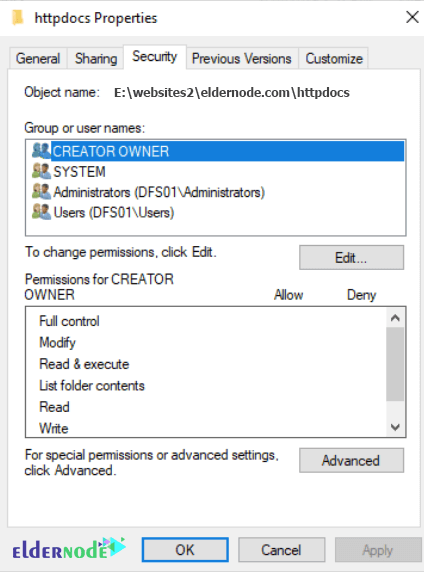
There are a number of security permissions set up on the folder that is unnecessary and potentially insecure.
To best secure a site, we recommend removing all but the SYSTEM and Administrators groups and adding the ApplicationPoolIdentity user (and possibly any other user you may require, such as an FTP user); however, to do this, you will need to disable inheritance.
To do this, click on Advanced, then click on Disable inheritance.
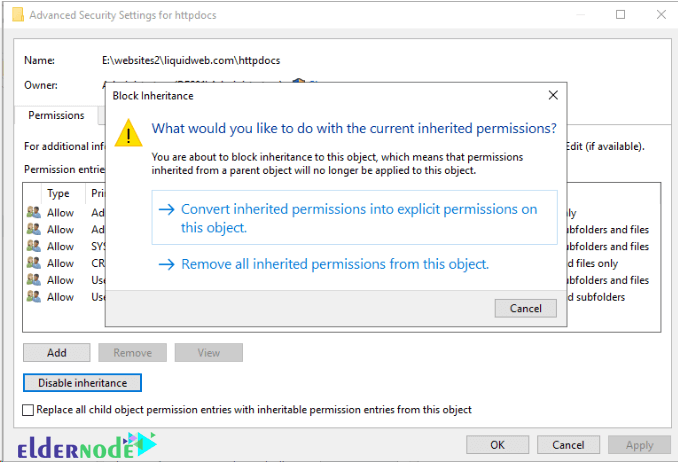
Here you will get a popup asking if you want to copy the current settings or start with no settings.
It is easier to copy the current settings and then remove the unnecessary permissions.
So select ConvertConcert inherited permissions into explicit permission on this object and then click OK.
At this point, to remove the unnecessary permissions, click Edit and remove everything other than the SYSTEM and Administrators groups.
Next, you need to add the ApplicationPoolIdentity user to this folder. To do this, click “Add…”.
Now, depending on your server configuration, you may get a pop-up asking for you to authenticate to an active directory domain.
Simply click the cancel button a few times until you get the Select Users of Groups screen shown below.
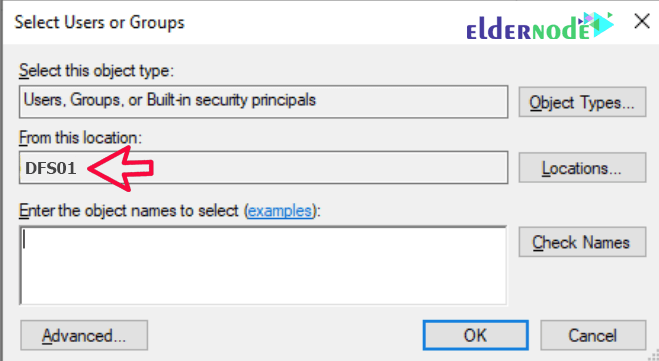
Now, you will want to make sure that the “Location” selected is your computer.
If it is not, click “Locations…” and select your computer.
VPS HOSTING PLANS
The ApplicationPoolIdentity user is a hidden user, so it is not possible to search for this user.
You will have to type the username to add it.
The username you will need to type is:
IIS AppPool\<applicationpoolname>Please see the following example and fill yours out accordingly:
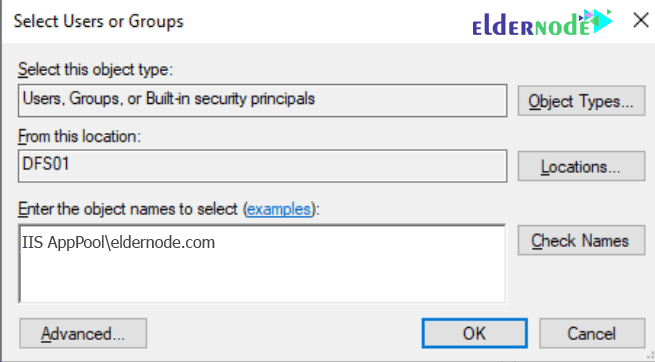
Type the user name, click OK.
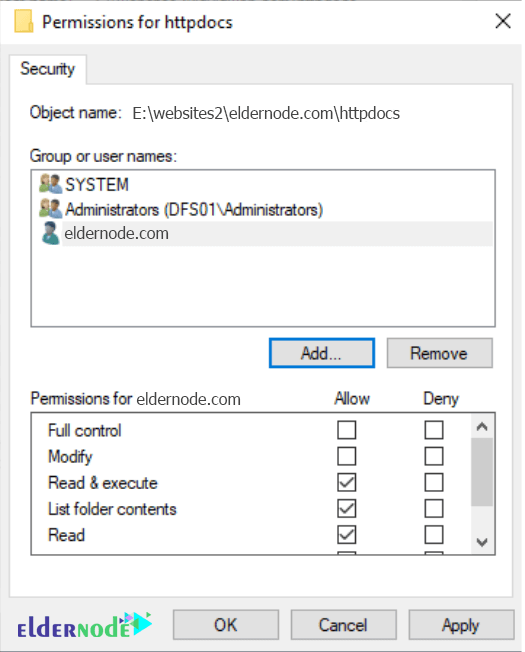
Now that you’ve added the user, which is by default only granted read permissions, you will want to verify your security settings look similar to the following image, and then click OK:
Dear user, we hope you would enjoy this tutorial, you can ask questions about this training in the comments section, or to solve other problems in the field of Eldernode training, refer to the Ask page section and raise your problem in it as soon as possible. Make time for other users and experts to answer your questions.
Goodluck.




The article was absolutely fantastic! Lot of great information which can be helpful in some or the other way.
Thank you for your encouraging comment, dear user.