Sometimes you just need an assistant to tell you what are your weaknesses, and how you should react to them. Yersinia is what you need to use the weaknesses in different network protocols. Since network administrations do not usually monitor the LAN unless receiving a problem report, attack occurrence is not surprising and several attacks on Layer 2 protocols could happen (Layer 2 is the second layer of the network, the second layer of OSI protocol). So, you can use Yersinia as a framework for performing layer 2 attacks, analyzes, and tests the deployed network and systems. While it consists of various layer 2 attacks exploiting the weaknesses of different layer-2 protocols, a pentester identifies the vulnerabilities in deep layer 2 of the network which is located in the data link layer like STP and CDP. Join us with this article to learn How To Install And Use Yersinia On Kali Linux. Do not miss the special offers of Eldernode Coupons and buy your own Linux VPS.
Table of Contents
Tutorial Install And Use Yersinia On Kali Linux
Yersinia is written in C language and is under the GNU General Public License version 2.0. It is designed to be used for penetration testing and attacks on layer-2 devices such as switches, DHCP servers spanning tree protocols, and so on. Using its GUI, Yersinia is able to make Denial Of Service (DOS) attacks on DHCP simple and easy. Attacks are implemented for some network protocols such as:
- Spanning Tree Protocol
- Cisco Discovery Protocol
- Dynamic Trunking Protocol
- Dynamic Host Configuration Protocol
- Host Standby Router Protocol
- 802.1q
- 802.1x
- Inter-Switch Link Protocol
- VLAN Trunking Protocol
Yersinia Options:
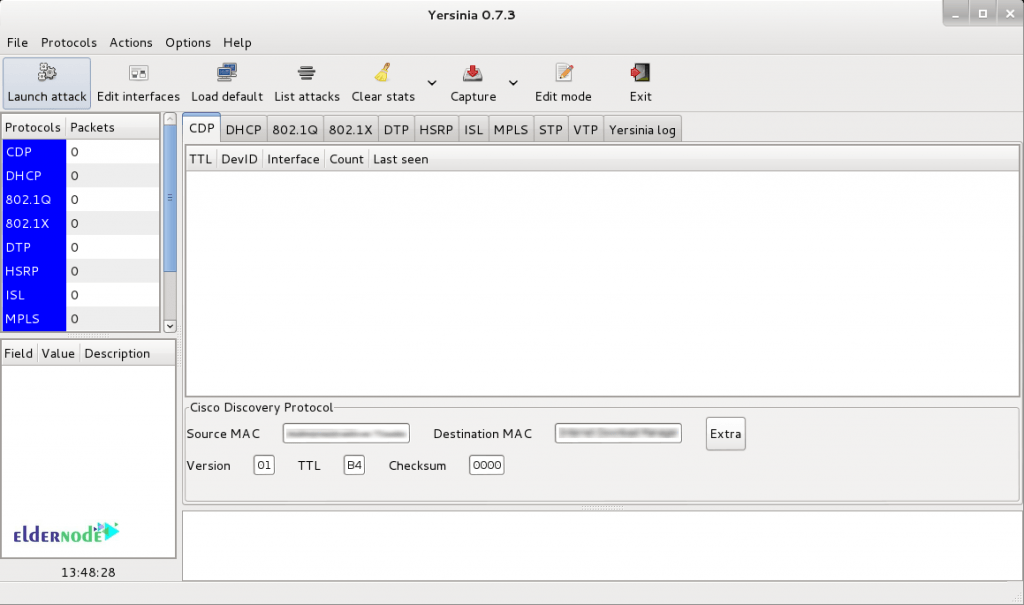
-h, --help [Help screen.]-V, --Version [Program version.]-G [Start a graphical GTK session.]-I, --interactive [Start an interactive ncurses session.]-D, --daemon [Start the network listener for remote admin (Cisco CLI emulation).]-d [Enable debug messages.]-l logfile [Save the current session to the file logfile. If logfile exists, the data will be appended at the end.]-c conffile [Read/write configuration variables from/to conffile.]-M [Disable MAC spoofing.]GTK GUI
The GTK GUI (-G) is a GTK graphical interface with all of the yersinia powerful features and a professional 'look and feel'. NCURSES GUI
The ncurses GUI (-I) is a ncurses (or curses) based console where the user can take advantage of yersinia powerful features. Press 'h' to display the Help ScreenNETWORK DAEMON
The Network Daemon (-D) is a telnet based server (ala Cisco mode) that listens by default in port 12000/tcp waiting for incoming telnet connections. It supports a CLI similar to a Cisco device where the user (once authenticated) can display different settings and can launch attacks without having yersinia running in her own machine (especially useful Windows users). Install Yersinia On Kali Linux
By default, Yersinia is not available in Kali 2020. It is available in two versions, Terminal and Graphical. However, it is possible to install this tool by a single command and you do not need to pass several steps to do this. Use the command below to install it on Kali.
sudo apt-get install yersiniaNow, you installed yersinia and any packages it needs.
To install the dependencies, type:
sudo apt-get installAlso, you can use its graphical version by typing:
yersinia -GYersinia Usage Example
How to uninstall Yersinia
In case you need to remove yersinia, you should just run the following command:
sudo apt-get remove yersiniaIn this way, you will remove just the yersinia packages.
But if you need to uninstall yersinia and its dependencies, type the command below:
sudo apt-get remove --auto-remove yersiniaCertainly, by executing the above command, you will remove the package of yersinia and all other dependant packages.
How to purge the configuration of data
You can also delete the local/configured files. Use the command below to do this.
sudo apt-get purge yersiniaOR
sudo apt-get purge --auto-remove yersiniaNote: Above all, please be aware that you cannot restore the purged config/data if you reinstall the package.
Conclusion
In this article, you learned How To Install And Use Yersinia On Kali Linux. From now on you can use the coolest layer 2 hacking tool. Start disguising packets of multiple protocols with this intrusion tool. Yersinia helps the pentester to check the power of layer-2 protocols configuration. In case you are interested to read more, find our related articles on How To Configure BeEF On Ubuntu 20.04 LTS.