
TLS, or transport layer security, and its predecessor SSL, which stands for secure sockets layer, are web protocols used to wrap normal traffic in a protected, encrypted wrapper.
Using this technology, servers can send traffic safely between servers and clients without the possibility of messages being intercepted by outside parties. The certificate system also assists users in verifying the identity of the sites that they are connecting with. Do not miss the most powerful Linux hosting to enjoy working with your studies.
To let this tutorial work better, please consider the below Prerequisites:
A non-root user with sudo privileges
To set up, follow our Initial server setup on Debian 10.
You will also need to have the Apache webserver installed. To see the details, you can follow our guide on setting up LAMP on Debian 10.
Before starting and follow the steps of this tutorial, please notice that A self-signed certificate will encrypt communication between your server and any clients. However, because it is not signed by any of the trusted certificate authorities included with web browsers, users cannot use the certificate to validate the identity of your server automatically.
A self-signed certificate may be appropriate if you do not have a domain name associated with your server and for instances where an encrypted web interface is not user-facing. If you do have a domain name, in many cases it is better to use a CA-signed certificate. You can find out how to set up a free trusted certificate with the Let’s Encrypt project here.
Table of Contents
Tutorial Create a Self-Signed SSL Certificate for Apache in Debian 10
After completing the prerequisites, you can walk through this guide and learn how to Create a Self-Signed SSL Certificate for Apache in Debian 10.
1- How To Create the SSL Certificate
Since the TLS/SSL works by using a combination of a public certificate and a private key, the SSL key is kept secret on the server and used to encrypt content sent to clients. The SSL certificate is publicly shared with anyone requesting the content. It can be used to decrypt the content signed by the associated SSL key.
So, to create a self-signed key and certificate pair with OpenSSL:
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/apache-selfsigned.key -out /etc/ssl/certs/apache-selfsigned.crtAs you will be asked a series of questions, let’s take a look at what is happening in the command you are issuing to help you go over that.
openssl: This is the basic command-line tool for creating and managing OpenSSL certificates, keys, and other files.
req: This subcommand specifies that you want to use X.509 certificate signing request (CSR) management. The “X.509” is a public key infrastructure standard that SSL and TLS adheres to for its key and certificate management. You want to create a new X.509 cert, so we are using this subcommand.
-x509: This further modifies the previous subcommand by telling the utility that you want to make a self-signed certificate instead of generating a certificate signing request, as would normally happen.
-nodes: This tells OpenSSL to skip the option to secure our certificate with a passphrase. You need Apache to be able to read the file, without user intervention, when the server starts up. A passphrase would prevent this from happening because we would have to enter it after every restart.
-days 365: This option sets the length of time that the certificate will be considered valid. you set it for one year here.
-newkey rsa:2048: This specifies that you want to generate a new certificate and a new key at the same time. You did not create the key that is required to sign the certificate in a previous step, so you need to create it along with the certificate. The rsa:2048 portion tells it to make an RSA key that is 2048 bits long.
-keyout: This line tells OpenSSL where to place the generated private key file that you are creating.
-out: This tells OpenSSL where to place the certificate that you are creating.
These options will create both a key file and a certificate. You will be asked a few questions about our server in order to embed the information correctly in the certificate.
Try to fill out the prompts appropriately. The most important line is the one that requests the Common Name (e.g. server FQDN or YOUR name). You need to enter the domain name associated with your server or, more likely, your server’s public IP address.
The entirety of the prompts will be as below output.
Country Name (2 letter code) [AU]:US State or Province Name (full name) [Some-State]:New York Locality Name (eg, city) []:New York City Organization Name (eg, company) [Internet Widgits Pty Ltd]:Bouncy Castles, Inc. Organizational Unit Name (eg, section) []:Ministry of Water Slides Common Name (e.g. server FQDN or YOUR name) []:server_IP_address Email Address []:admin@your_domain.coPoint: Both of the files you created will be placed in the appropriate subdirectories under /etc/ssl.
2- How To Configure Apache to Use SSL
When have created our key and certificate files under the /etc/ssl directory, you just need to modify our Apache configuration to take advantage of these.
By this, you will make a few adjustments to your configuration:
You will create a configuration snippet to specify strong default SSL settings.
You will modify the included SSL Apache Virtual Host file to point to our generated SSL certificates.
(Recommended) You will modify the unencrypted Virtual Host file to automatically redirect requests to the encrypted Virtual Host.
After all, if you verify, you would have a secure SSL configuration.
Let’s Create an Apache Configuration Snippet with Strong Encryption Settings
To begin this step, you will create an Apache configuration snippet to define some SSL settings. This will set Apache up with a strong SSL cipher suite and enable some advanced features that will help keep our server secure. The parameters we will set can be used by any Virtual Hosts enabling SSL.
Create a new snippet in the /etc/apache2/conf-available directory. We will name the file ssl-params.conf to make its purpose clear:
sudo nano /etc/apache2/conf-available/ssl-params.confAlso, you can copy the provided settings in their entirety. You will just make one small change to this and disable the Strict-Transport-Security header (HSTS).
Preloading HSTS provides increased security but can have far-reaching consequences if accidentally enabled or enabled incorrectly. In this guide, we will not enable the settings, but you can modify that if you are sure you understand the implications.
But before deciding, take a moment to read up on HTTP Strict Transport Security, or HSTS, and specifically about the “preload” functionality.
Then, paste the following configuration into the ssl-params.conf file you opened:
SSLCipherSuite EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDH SSLProtocol All -SSLv2 -SSLv3 -TLSv1 -TLSv1.1 SSLHonorCipherOrder On Disable preloading HSTS for now. You can use the commented out header line that includes the "preload" directive if you understand the implications. Header always set Strict-Transport-Security "max-age=63072000; includeSubDomains; preload" Header always set X-Frame-Options DENY Header always set X-Content-Type-Options nosniff Requires Apache >= 2.4 SSLCompression off SSLUseStapling on SSLStaplingCache "shmcb:logs/stapling-cache(150000)" Requires Apache >= 2.4.11 SSLSessionTickets OffYou can save and close the file when you are finished.
Let’s Modify the Default Apache SSL Virtual Host File
Next, let’s modify /etc/apache2/sites-available/default-ssl.conf, the default Apache SSL Virtual Host file. If you are using a different server block file, substitute its name in the commands below.
Before you go any further, let’s back up the original SSL Virtual Host file:
sudo cp /etc/apache2/sites-available/default-ssl.conf /etc/apache2/sites-available/default-ssl.conf.bakNext, open the SSL Virtual Host file to make adjustments:
sudo nano /etc/apache2/sites-available/default-ssl.confInside, with most of the comments removed, the Virtual Host block should look something like this by default:
<IfModule mod_ssl.c> <VirtualHost _default_:443> ServerAdmin webmaster@localhost DocumentRoot /var/www/html ErrorLog ${APACHE_LOG_DIR}/error.log CustomLog ${APACHE_LOG_DIR}/access.log combined SSLEngine on SSLCertificateFile /etc/ssl/certs/ssl-cert-snakeoil.pem SSLCertificateKeyFile /etc/ssl/private/ssl-cert-snakeoil.key <FilesMatch "\.(cgi|shtml|phtml|php)$"> SSLOptions +StdEnvVars </FilesMatch> <Directory /usr/lib/cgi-bin> SSLOptions +StdEnvVars </Directory> </VirtualHost> </IfModule>You will be making some minor adjustments to the file. You will set the normal things you would want to adjust in a Virtual Host file (ServerAdmin email address, ServerName, etc.), and adjust the SSL directives to point to our certificate and key files. Again, if you’re using a different document root, be sure to update the DocumentRoot directive.
You would see your server block as below when you make these changes.
<IfModule mod_ssl.c> <VirtualHost _default_:443> ServerAdmin [email protected] ServerName server_domain_or_IP DocumentRoot /var/www/html ErrorLog ${APACHE_LOG_DIR}/error.log CustomLog ${APACHE_LOG_DIR}/access.log combined SSLEngine on SSLCertificateFile /etc/ssl/certs/apache-selfsigned.crt SSLCertificateKeyFile /etc/ssl/private/apache-selfsigned.key <FilesMatch "\.(cgi|shtml|phtml|php)$"> SSLOptions +StdEnvVars </FilesMatch> <Directory /usr/lib/cgi-bin> SSLOptions +StdEnvVars </Directory> </VirtualHost> </IfModule>You can save and close the file when you are finished.
How To Modify the HTTP Host File to Redirect to HTTPS (Recommended)
As you see, the server will provide both unencrypted HTTP and encrypted HTTPS traffic. For better security, it is recommended in most cases to redirect HTTP to HTTPS automatically. If you do not want or need this functionality, you can safely skip this section.
Open the /etc/apache2/sites-available/000-default.conf file to adjust the unencrypted Virtual Host file to redirect all traffic to be SSL encrypted.
sudo nano /etc/apache2/sites-available/000-default.confInside, within the VirtualHost configuration blocks, add a Redirect directive, pointing all traffic to the SSL version of the site:
<VirtualHost *:80> . . . Redirect "/" "https://your_domain_or_IP/" . . . </VirtualHost>You can save and close the file when you are finished.
That’s all of the configuration changes you need to make to Apache. Next, you will discuss how to update firewall rules with ufw to allow encrypted HTTPS traffic to your server.
3- How To Adjust the Firewall
As we asked you to have the ufw firewall enabled in the prerequisite, you might need to adjust the settings to allow for SSL traffic. Fortunately, when installed on Debian 10, ufw comes loaded with app profiles which you can use to tweak your firewall settings.
To see the available profiles, use the following command:
sudo ufw app listAvailable applications: . . . WWW WWW Cache WWW Full WWW Secure . . .Type the below command to see the current setting.
sudo ufw statusStatus: active To Action From -- ------ ---- OpenSSH ALLOW Anywhere WWW ALLOW Anywhere OpenSSH (v6) ALLOW Anywhere (v6) WWW (v6)To additionally let in HTTPS traffic, allow the “WWW Full” profile and then delete the redundant “WWW” profile allowance:
sudo ufw allow 'WWW Full' sudo ufw delete allow 'WWW'And your status should look like this now:
sudo ufw statusStatus: active To Action From -- ------ ---- OpenSSH ALLOW Anywhere WWW Full ALLOW Anywhere OpenSSH (v6) ALLOW Anywhere (v6) WWW Full (v6) ALLOW Anywhere (v6)With your firewall configured to allow HTTPS traffic, you can move on to the next step where you’ll go over how to enable a few modules and configuration files to allow SSL to function properly.
4- How To Enable the Changes in Apache
At this step, you can enable the SSL and headers modules in Apache, enable our SSL-ready Virtual Host, and then restart Apache to put these changes into effect, as you have made your changes and adjusted our firewall.
So let’s enable mod_ssl, the Apache SSL module, and mod_headers, which is needed by some of the settings in our SSL snippet, with the a2enmod command:
sudo a2enmod ssl sudo a2enmod headersAnd type the command below to enable your SSL Virtual Host with the a2ensite
sudo a2ensite default-sslYou will also need to enable your ssl-params.conf file, to read in the values you’ve set:
sudo a2enconf ssl-paramsBy this, the site and the necessary modules are enabled. Also, you should check to make sure that there are no syntax errors in our files. Do this by typing:
sudo apache2ctl configtestSyntax OKAs long as your output has Syntax OK in it, then your configuration file has no syntax errors and you can safely restart Apache to implement the changes:
sudo systemctl restart apache2With that, your self-signed SSL certificate is all set. You can now test that your server is correctly encrypting its traffic.
5- How To Test Encryption
At this point, you’re ready to test your SSL server.
Open your web browser and type https:// followed by your server’s domain name or IP into the address bar:
https://server_domain_or_IPBecause the certificate you created isn’t signed by one of your browser’s trusted certificate authorities, you will likely see a scary looking warning like the one below:
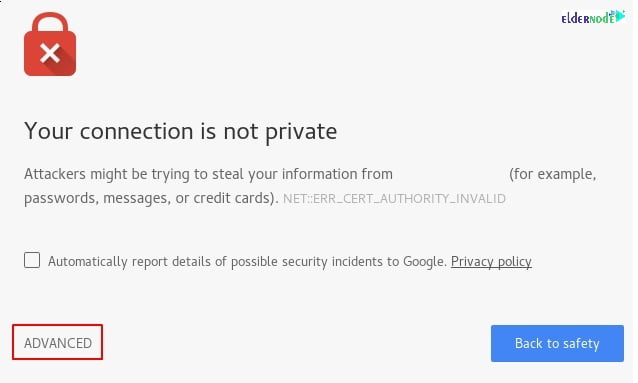
But be aware that this is very expected and normal. you are only interested in the encryption aspect of our certificate, not the third party validation of our host’s authenticity. Click ADVANCED and then the link provided to proceed to your host anyways:
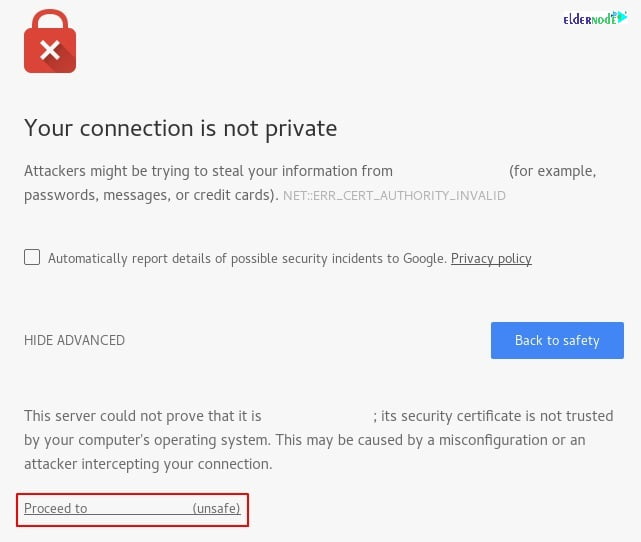
Check to be taken to your site. If you look in the browser address bar, you will see a lock with an “x” over it or another similar “not secure” notice. In this case, this just means that the certificate cannot be validated. It is still encrypting your connection.
If you configured Apache to redirect HTTP to HTTPS, you can also check whether the redirect functions correctly:
http://server_domain_or_IPBy receiving these results in the same icon, your redirect has worked correctly. However, the redirect you created earlier is only a temporary redirect. If you’d like to make the redirection to HTTPS permanent, continue on to the final step.
6- How To Change to a Permanent Redirect
Once, you ensure that redirect has worked correctly and you are sure you want to allow only encrypted traffic, modify the unencrypted Apache Virtual Host again to make the redirect permanent.
Open your server block configuration file again:
sudo nano /etc/apache2/sites-available/000-default.confNow, find the Redirect line we added earlier. Add permanent to that line, which changes the redirect from a 302 temporary redirect to a 301 permanent redirect:
<VirtualHost *:80> . . . Redirect permanent "/" "https://your_domain_or_IP/" . . . </VirtualHost>Now, you can save and close the file.
Use the following command to check your configuration for syntax errors:
sudo apache2ctl configtestIn case this command doesn’t report any syntax errors, you can restart Apache:
sudo systemctl restart apache2By this, you can make the redirect permanent, and your site will only serve traffic over HTTPS.
Conclusion
In this article, you learned how to Create a Self-Signed SSL Certificate for Apache in Debian 10. And of course, you have configured your Apache server to use strong encryption for client connections. This will allow you to serve requests securely and will prevent outside parties from reading your traffic. In case you are interested in learning more about this subject, follow our related articles on Tutorial Install SSL Certificate on IIS Web Server AND How to install Apache Web Server on Debian 10.



Is it nesseccary to have an RSA keypair to create SSL in Linux?
Yes, sure. After that you need to extract the private key into the ‘’httpd’’ folder.
What about private key in CSR?
To generate a private key in CSR, run the following commands after login to your account using SSH. It also contains the public key that will be included in the certificate.
openssl req -new -newkey rsa:2048 -nodes -keyout server.key -out server.csrIs it possible to fix a self-signed certificate error?
Yes, sure. First, you need to make your site certificate trusted on your client browser. You can use the following two ways: A typical OS comes with popular trusted roots (root certificates) of some companies.
Why is Certificate not trusted?
The main reason is that the certificate installation was not properly completed on the server.
thank you. I need to resolve a certificate issue.
Follow the below path to do this:
• In Windows Internet Explorer, click Continue to this website (not recommended). …
• Click the Certificate Error button to open the information window.
• Click View Certificates, and then click Install Certificate.
• On the warning message that appears, click Yes to install the certificate